| Email Delivery | ||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Transport | ||||||||||||||||||||||||||||||||||||||||
|
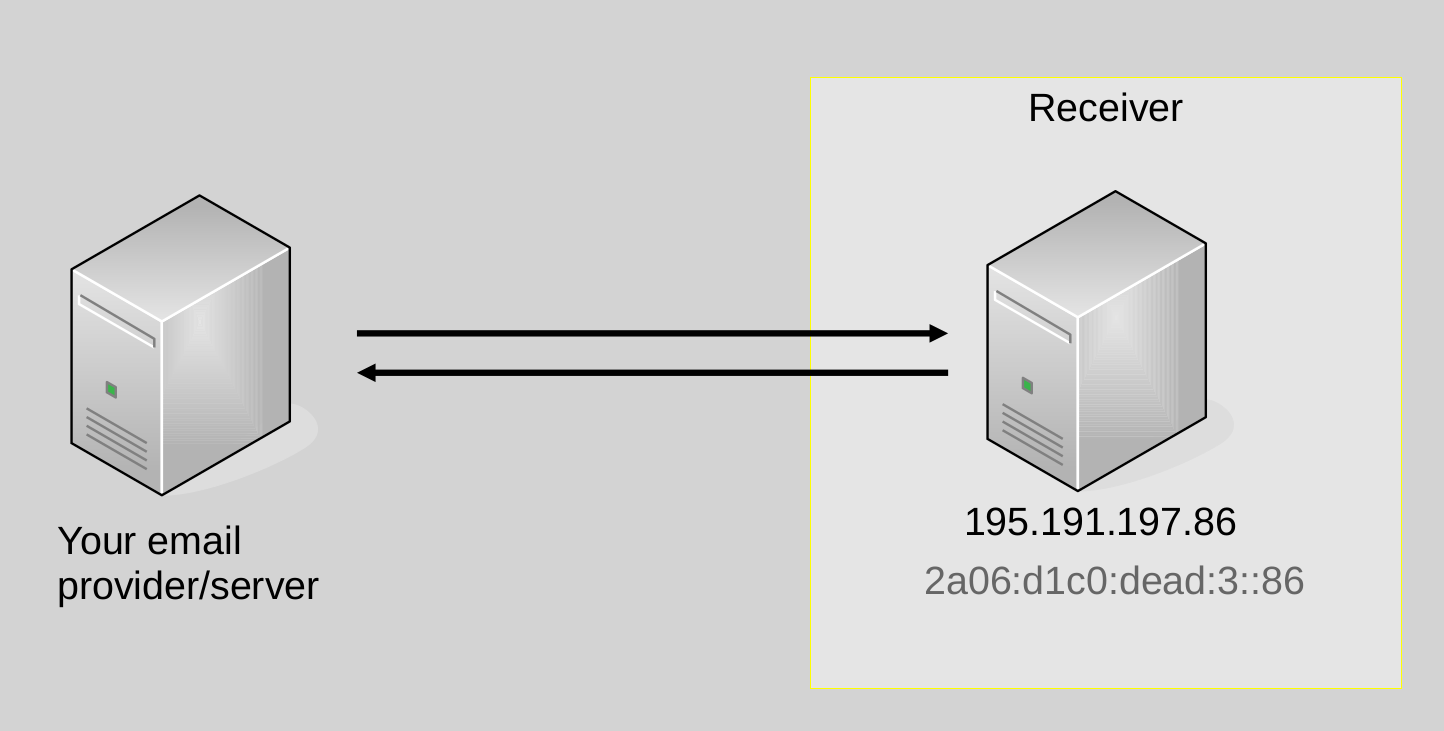
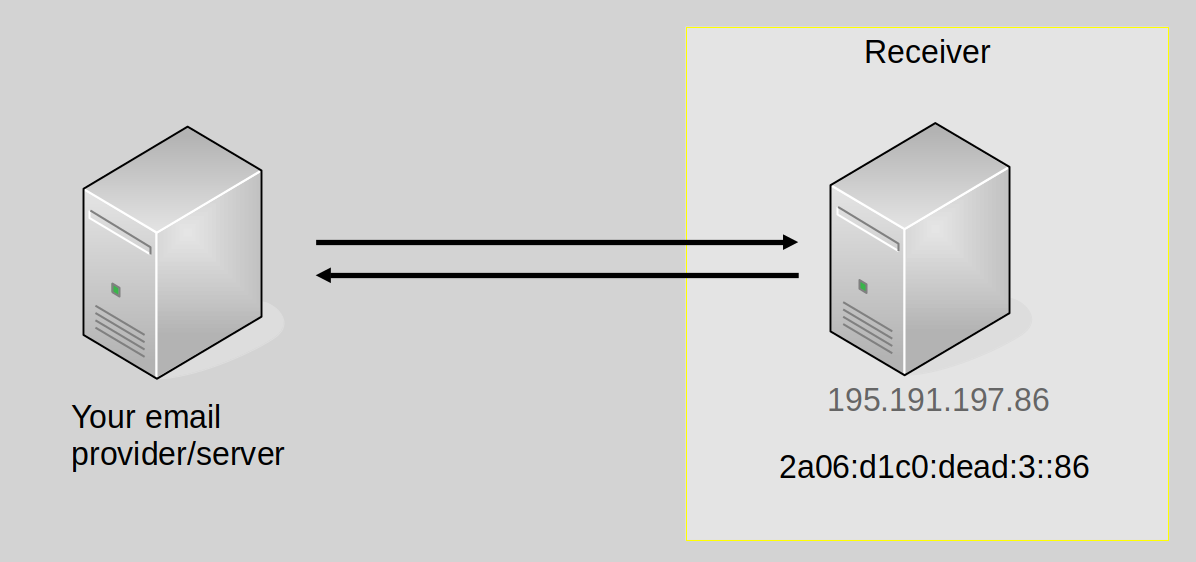
When sending emails, your mailprovider supports IPv4 email delivery.
|
||||||||||||||||||||||||||||||||||||||||
|
When sending emails, your mailprovider supports IPv6 email delivery. While receiving emails over IPv6 poses new challenges to spam prevention, IPv4 is running out, and it is time to get IPv6 ready! |
||||||||||||||||||||||||||||||||||||||||
|
Greylisting is an anti-spam measure. It leverages that many spammers do not queue emails by sending a temporary error to any unknown combination of sender IP address, MAIL FROM, and RCPT TO. A valid sender will try to redeliver the email during a certain timeframe (usually 24 hours to a few days). When sending emails, your mailprovider attempts re-delivery (supports sending to servers using greylisting). |
||||||||||||||||||||||||||||||||||||||||
| TLS / Encryption | ||||||||||||||||||||||||||||||||||||||||
✅ 💡 |
||||||||||||||||||||||||||||||||||||||||
|
Note: Plaintext delivery is supported; While technically insecure, there are still some mailservers in production that do not support TLS, so it might make sense to allow plaintext delivery.Your email provider/server supports emails in cleartext if the STARTTLS option is not presented by the receiver or stripped from the communication. |
||||||||||||||||||||||||||||||||||||||||
✅ 💡 |
||||||||||||||||||||||||||||||||||||||||
|
Note: The mailserver supports medium strength ciphers; While a little less secure, this improves deliverability over just supporting strong ciphers.Transport encryption protects emails from passive eavesdropping on the way from the sender to the receiver. Still both the sending and the receiving email servers and every email server on the path from the sender to the receiver sees the email in cleartext.
|
||||||||||||||||||||||||||||||||||||||||
✅ 💡 |
||||||||||||||||||||||||||||||||||||||||
|
Note: Opportunistic encryption (accepting any certificate) is supported; While technically insecure, there are still some mailservers in production that do not support validated TLS connections, so opportunistic encryption is better than nothing.Transport encryption for email is mostly opportunistic. Expired and self-signed certificates are treated as valid. In case of an error the SMTP connection will fall back to plaintext. However, this makes email delivery vulnerable to spoofing and Monkey-in-the-middle (MITM) attacks. To measure how your email provider/server treats invalid certificates, mail-tls-invalid.measurement.email-security-scans.org presents an expired certificate with a non-matching CN entry. Your email provider/server supports |
||||||||||||||||||||||||||||||||||||||||
|
Domain-based Authentication of Named Entities (DANE) is a more recent standard that allows to publish certificate information in DNS with TLSA records. A sender is then able to verify the certificate of the receiving email server based on the information in the TLSA record. This also indicates that the receiver supports encryption before initiating a STARTTLS connection. To guaratanee validity of the certificate information, DANE only works in combination with DNSSEC.
References: APNIC - Better mail security with DANE for SMTP [EN] |
||||||||||||||||||||||||||||||||||||||||
|
MTA-Strict Transport Security enables strict transport encryption for domains without DNSSEC.
To test your inbound MTA-STS policy (and more!), run the e-mail test from Internet.nl: Internet.nl E-Mail Test [EN] |
||||||||||||||||||||||||||||||||||||||||
✅ 💡 |
||||||||||||||||||||||||||||||||||||||||
|
Your mailserver sends out TLS reports, and we received a report at 2026-04-23T00:05:28 (Download)
|
||||||||||||||||||||||||||||||||||||||||
| DNS | ||||||||||||||||||||||||||||||||||||||||
| DNS Resolution | ||||||||||||||||||||||||||||||||||||||||
|
|
||||||||||||||||||||||||||||||||||||||||
|
The DNS resolver, your email provider/server relies on, supports DNS resolution over IPv6. |
||||||||||||||||||||||||||||||||||||||||
|
The DNS resolver your email provider/server relies on, supports DNSSEC. |
||||||||||||||||||||||||||||||||||||||||
| DNS Configuration of Your Zones/Mailservers | ||||||||||||||||||||||||||||||||||||||||
|
Here, we test whether a recursive DNS server that only supports IPv6 can resolve all names/zones relevant for your email setup. All zones your mailsetup depends upon are IPv6 resolvable. |
||||||||||||||||||||||||||||||||||||||||
|
Some names needed for email delivery are not DNSSEC signed. This is important to verify the authenticity and integrity of SPF, DKIM, DANE, reverse DNS, and DMARC entries.
|
||||||||||||||||||||||||||||||||||||||||
| Sending Host Configuration & Authenticated Sender | ||||||||||||||||||||||||||||||||||||||||
|
|
||||||||||||||||||||||||||||||||||||||||
|
Your SPF policy is valid and needs less than 10 additional DNS queries.
|
||||||||||||||||||||||||||||||||||||||||
|
DomainKeys Identified Mail (DKIM) allows claiming responsibility for an email by cryptographically sigining it. It prevents forgery and spam. Your mailsetup uses DKIM. All DKIM signatures are valid and in good order.
|
||||||||||||||||||||||||||||||||||||||||
|
Domain-based Message Authentication, Reporting and Conformance (DMARC) was introduced to let the receiver know, how to react to SPF and DKIM validation results and enable reporting.
|
||||||||||||||||||||||||||||||||||||||||
|
You have the following addresses configured to receive DMARC reports:
|
||||||||||||||||||||||||||||||||||||||||
|
Your mail-setup is IPv6 ready! IPv6 mail delivery, DNS resolution, and IPv6 support for all zones you depend on works! |
||||||||||||||||||||||||||||||||||||||||
| Message Basics | ||||||||||||||||||||||||||||||||||||||||
|
No duplicate headers found. |
||||||||||||||||||||||||||||||||||||||||
|
No missing headers found. |
||||||||||||||||||||||||||||||||||||||||
|
Envelope From and Mail From domains always match. |
||||||||||||||||||||||||||||||||||||||||
 References:
References: